I have identified some potential security vulnerability while using Dropbox. I believe this issue may pose a risk to the protection of user data, and I would like to promptly share my findings with you to help enhance the security of Dropbox.
Vulnerability Description:
Dropbox implements a Passcode mechanism to lock the app, but I find the Passcode fails to be invoked when some activities are resumed. Vulnerable Activities are listed as follows.
ID Activity
1 GroupedPhotoPreviewActivity
2 BulkRenameActivity
The detailed instructions for triggering the vulnerability are provided in the attachment.
These vulnerabilities may pose a risk of sensitive data leakage. As you can see from the attachment, some privacy user data, such as personal photos, are clearly displayed on the screen without passcode protection.
I hope this issue can be investigated and addressed as soon as possible to improve the application's security and protect user data. Please contact me for more details or any assistance needed to confirm this vulnerability.
I look forward to your prompt response!
Attachment:
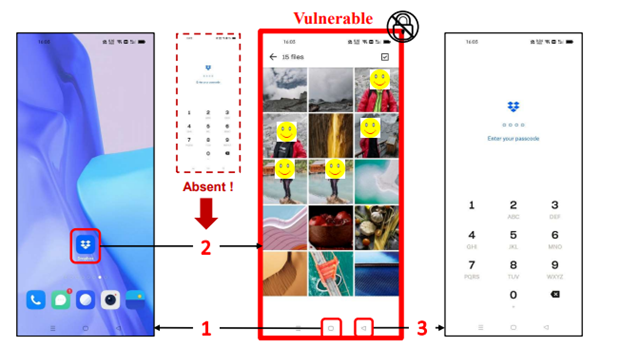
Take GroupedPhotoPreviewActivity as an example:
The middle page is GroupedPhotoPreviewActivity.
when Dropbox goes to the background (❶) and then is awakened, this activity is switched to be running (❷). Unfortunately, the interface lock is not triggered when this activity is resumed.
While navigating to other interfaces activates the interface lock (❸), this particular interface allows direct access to private photos stored within the cloud drive.